Data is everywhere, it is a piece of information, particularly facts and numbers, gathered to analyze and make significant business decisions. As it is available easily, it’s required to protect the data from cyberattacks.
Like most businesses, if your company is also dealing with data, then you must have an effective data resiliency strategy. But you might ask, what is it exactly?
It refers to a business’s ability to quickly retrieve its data from loss or cyberattacks and keep the organization’s operations going efficiently.
And at the same time rigorously monitoring and protecting the data. However, it is vital to note that resilience strategy is not the same as backing up data.
Regardless, it is necessary to have a backup and recovery plan. Understanding the principles of data resiliency is necessary.
In this article, we will guide and provide information on the principles that need to be known to utilize an effective data resilience strategy.
Importance of Data Resilience
Data resilience is a significant process that is required for multiple reasons, especially because of an increasing number of cyberattacks. It is accessible and available to authorized units, and if the data is resilient, then it will not be manipulated by a hacker easily during a cyberattack.
So, it is necessary to have a Data resilience strategy to protect the information from getting deleted or modified to maintain the data integrity and keep it safe.
A Look at the Principles of an Effective Data Resiliency Strategy
So, all effective data resiliency strategies have something in common. Each one is proactive, which means the strategy isn’t designed to kick in after a disaster happens. Instead, these strategies work to prevent disasters that lead to recovery efforts.
Yes, backing up the data is a part of most strategies, but it’s not all that’s included in the plan. So, what to include in a data resiliency strategy? Here are a few principles you don’t want to miss.
Robust Cybersecurity is a Must
Okay if you’re dealing with data, then be aware of the various rules and regulations. These vary across industries, and even states can have different laws on the books. An example is California.
The state is adamant that all consumer personal information must be protected. So, if you’re doing business in California, everyone must follow state guidelines even if you’re headquartered somewhere else.
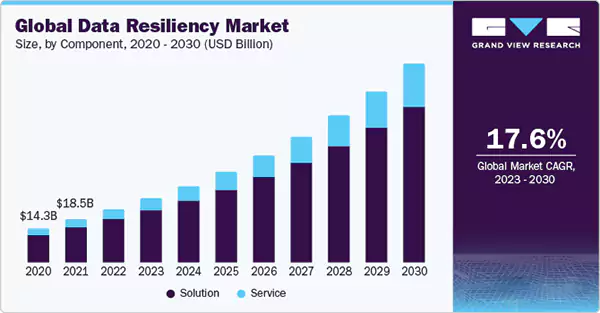
The graph below represents the increasing market of data resilience globally.
Your cybersecurity protocols must meet industry standards. It includes possible occurrences of vulnerabilities and prevention of data from security breaches.
If you need some guidance on industry standards or tips on creating robust cybersecurity protocols, a good resource is the National Institute of Standards and Technology or NIST.
There, you can discover frameworks that can help in creating a robust cybersecurity plan.
Some things to consider in your cybersecurity plan include:
- Conducting regular system audits: These audits should be intended to discover any risk and identification of any potential threats.
- Implementing robust access controls: Remember, you may not want everyone accessing all of your data. To ensure staff have the access necessary for them to perform their roles, implement multifactor authentication practices.
- Insertion of programs: Installation of firewalls, antivirus software, and
procedures to discover interruptions. By adapting these methods you can get protection against malware, phishing, and hacking.
Take a Look at Your Disaster Recovery Plan
Hopefully, your business has a disaster recovery plan in place. Even if you have not yet done it, do it now to create an effective one.
A recovery plan should primarily focus on minimizing downtimes to get things back up and running after a natural or man-made disaster.
Keep in mind, your plan should account for both man-made and natural disasters.
What should you include in the plan? This can vary depending on an organization’s needs, however, most plans account for both data and system recovery.
Don’t forget to test the retrieval plan. This plan has to be tested, at least twice a year. Some companies run a test every quarter.
Be prepared to update the recovery plan as technology advances.
Create a Backup Solution

Even if you have an effective disaster recovery plan, still there are chances to lose part of your data if you don’t have a useful backup solution.
An effective example to follow is keeping three copies of your data; store two copies onsite and the third in the cloud or similar offsite storage solution. Yes, it might sound redundant to keep three copies. However, it’s also an effective way of ensuring you never lose vital information.
Something else to consider is using an encryption key, which can prevent any unauthorized changes that can occur during a disaster—for example, a security breach. Hackers may alter or delete data. Your data gets added defense with an encryption key.
Take Advantage of the Cloud,
Yes, there can be concerns about data safety in the cloud, but this often depends on the type of platform. You can decide to store the information in a public, private, or hybrid cloud.
Public clouds can leave data slightly vulnerable, yet it’s different when you use a private one. With a private cloud, only you and other authorized personnel can access it.
Do you know?
Around 2.5 quintillion bytes worth of data is generated each day.
The cloud is also scalable, which means you can store large batches of data or only small amounts.
Another benefit of storage of data on the cloud is the automated backup feature. The cloud automatically backs up the information, so don’t worry about this step.
However, on the safe side, keeping a copy in another location it’s still a good idea.
Segmentation is key
Segmentation of Data is considered as a classified process, intended for circumstances in which current or future data of IT gets stolen or lost. This method helps in prioritizing the files that are required to be restored immediately in case of any unfortunate event.
It is necessary to note that data segmentation should be done before any disturbance happens. It helps in dealing with any unforeseen turn of events, so the earlier, the better.
Keeping Your Data Safe
Securing your data is indeed a relentless task, yet its significance cannot be overstated.
Implementation of a robust resilience strategy not only streamlines the protection process but also guarantees that the information remains accessible, even in the face of disruptions.
This approach encompasses regular backups, redundancy systems, and disaster recovery plans, all of which are pivotal in minimizing downtime and data loss.